Absolute Applications
Cash Receipts and Accessibility – An SoD Tale of Dependency
Submitted by Cam Larner on Sunday, 06/17/2019 - 5:31 pm 0 commentWritten by Cam LarnerPresidentAbsolute Technologies, Inc. Earlier this year, a customer contacted me to report that SoD Violations Manager for Oracle E-Business Suite was inaccurately identifying that a user could perform transactions via the Receivables Cash Receipts form function, technically known as AR_ARXRWMAI_BATCH. She
Read More
Role Based Access Controls in R12 – Pros & Cons
Submitted by Cam Larner on Sunday, 10/25/2018 - 6:37 pm 0 commentThinking of deploying User Management’s RBAC (Role Based Access Controls) in your EBS R12 instance? RBAC, in principle, has been touted as a best practice for efficiently achieving SoD compliance in systems prone to access risk. Advocates assert that once configured, it requires less effort to maintain and provision
Read More
Achieve SoD Compliance with Cloud based User Access Controls
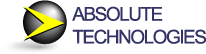
Submitted by Cam Larner on Sunday, 08/15/2018 - 6:02 pm 0 commentOracle has announced end of support for GRC on R12, as it “encourages” customers to upgrade to Fusion. Concerned about your GRC investment? Why not consider Absolute’s Cloud based User Access Controls module for SoD Compliance, SoD Violations Manager? Whether you run EBS on R11, R12 or in the Cloud, it’s
Read More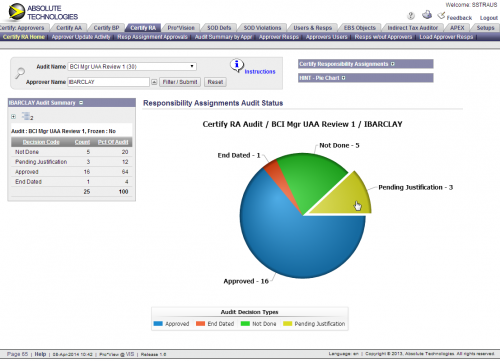
Certify Responsibility Assignments – Automate User Access Controls
Submitted by Cam Larner on Sunday, 03/15/2018 - 4:16 pm 2 commentsMany Oracle E-Business Suite customers periodically audit who has access to what EBS Responsibilities…manually! To automate user access controls in Oracle EBS, Absolute Technologies added Certify Responsibility Assignments™ (CRA) to its suite of GRC products. CRA empowers internal auditors and assignment approvers
Read More
Resolving Java Security Issues in Oracle E-Business Suite
Submitted by on Sunday, 07/01/2015 - 2:02 pm 0 commentA customer recently contacted me regarding issues connecting to Oracle EBS forms based modules (like SOD Violations Manager), in which new security settings in Java 7+ were preventing him from accessing the application. I advised him that he now needed to register the module’s URL as a trusted site in Java and in the
Read More